Hi@all,
It’s been quite a while since we had an article on this. I have connected the pfSense to the UCS LDAP server. I did it more or less as described in the old post:
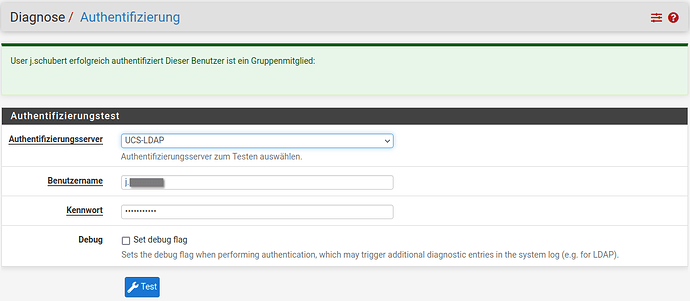
I have imported the UCS-CA from the Primary Director Node and configured the following authentication settings in pfSense:
Descriptive name: UCS-LDAP
Type: LDAP
Host name or IP address: srv01.lan.example.de
Port value: 7636
Transport: SSL/TLS Encrypted
Certificate authority of the peer: UCS RootCA
Protocol version: 3
Server timeout: 25
Search scope: One level
Base DN: dc=lan,dc=example,dc=de
Authentication containers: cn=users,dc=lan,dc=example,dc=de
Advanced search: [ ]
Bind anonymously: [ ]
Binding credentials: uid=ldapbind,cn=users,dc=lan,dc=example,dc=de
User name attribute: uid
Group name attribute: cn
Group member attribute: memberOf
RFC 2307 groups: [X]
Group object class: posixGroup
Shell Authentication Group DN: users
UTF8 encoding: [ ]
Changes to user names: [ ]
Allow unauthenticated bind: [ ]
The users who are allowed to use OpenVPN access on the pfSense are in the “openvpn” group in the USC. And I would like to restrict access to this group. To do this, I expand the advanced search and enter the following as a search filter:
(&(memberOf=cn=openvpn,cn=groups,dc=lan,dc=example,dc=de))
As soon as this filter is active, the test no longer works with a user from this group. Reference was made to this article in the first post:
This one is already a few years old. Are these steps still necessary for UCS 5.0.5?
Or is the error somewhere else?
with best
sven