Hallo zusammen,
ich habe ein paar Fragen an alle, die bereits einen UCS als Member einer samba4-AD-Domäne eingerichtet haben.
Wenn ich bei der Einrichtung des UCS “Einer bestehenden Active-Directory-Domäne beitreten” wähle um meiner bestehenden samba4-AD-Domäne (Debian 8 “Jessie”) beizutreten, schlägt dies aufgrund falscher Authentifizierung fehl (falscher Benutzername/Passwort). Bei der Einrichtung werden aber die richtigen Zugangsdaten des Domain-“Administrator”-Accounts angegeben.
Offensichtlich versucht der UCS sich mit seinem Rechnernamen und dem Passwort in der Datei /etc/machine.secret am DC anzumelden.
Sollte das grundsätzlich funktionieren? Soll der Computeraccount im Zuge der Einrichtung automatisch erstellt werden? Auch wenn ich das Maschinenkonto vorab im AD anlege, wird das machine.secret wohl kaum mit dem Kennwort des Computeraccounts im AD übereinstimmen?!
Ich kann jetzt natürlich manuell den Computeraccount anlegen und dessen Kennwort im AD entsprechend dem machine.secret setzen, aber das kann doch nicht die Standardlösung sein, oder?
Oder soll die Anmeldung am AD mittels Administrator-Account erfolgen durch Änderung der UCR-Variablen, wie:
ucr set connector/ad/ldap/binddn=Administrator
ucr set connector/ad/ldap/bindpw=/etc/univention/connector/password
touch /etc/univention/connector/password
chmod 600 /etc/univention/connector/password
echo -n "Administrator password" > /etc/univention/connector/password
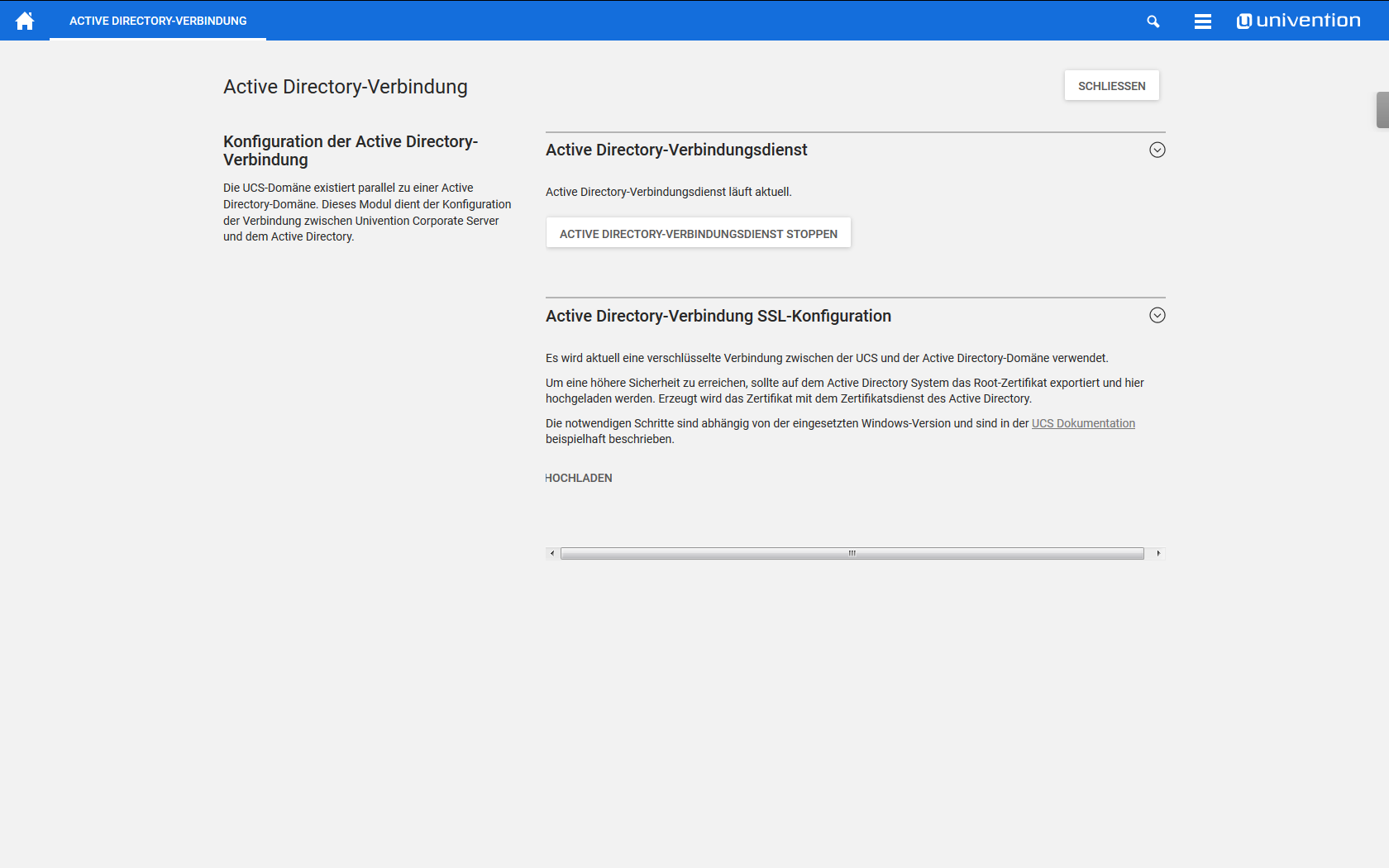
Und mit welchem Kommando reinitialisiere ich die Einrichtung der AD-Verbindung, wenn ich die Daten geändert habe, oder reicht ein systemctl restart univention-ad-connector?
Grüße, Hans