Problem:
For unknown reasons some of your users appear to have a expired password even though your password policies does not enforce password expiry.
Investigation:
The setting will be set via UDM with the attribute passwordexpiry:
udm users/user list --filter uid=egroupware-ucs5backup | grep -iE "passwordexpiry|dn"
DN: uid=egroupware-ucs5backup,cn=egroupware,dc=univention,dc=intranet
gidNumber: 5000
passwordexpiry: 2026-08-02
And will be triggert, if pwdChangeNextLogin was set.
udm users/user list --filter uid=egroupware-ucs5backup | grep -iE "passwordexpiry|dn|pwd"
DN: uid=egroupware-ucs5backup,cn=egroupware,dc=univention,dc=intranet
gidNumber: 5000
passwordexpiry: 2026-08-02
pwdChangeNextLogin: 0
The value for the UDM password expiry, will get directly from the LDAP attribute krb5PasswordEnd.
univention-ldapsearch -LLL uid=egroupware-ucs5backup | grep -iE "shadow|krb5password"
objectClass: shadowAccount
shadowLastChange: 20487
krb5PasswordEnd: 20260802000000Z
shadowMax: 179
Solution for OpenLDAP:
Disable the Posix and Kerberos expiry dates for all affected users.
Step 1
Check that password expiry policies configured in Univention Directory Manager (UDM) and Samba/AD are set to the same values. Please note that UDM policies and Samba/AD domain policies are not automatically synchronized because they have different design concepts: Different UDM policies may be assigned to different users (or containers) but in Samba/AD there is an additional global domain wide policy. If the values differ, the user experience may appear inconsistent.
Step 2
Use the DN from the user object and create an ldif file on the DC Master named user.ldif, which contains all user entries as shown below:
univention-ldapsearch -LLL uid=egroupware-ucs5backup dn
dn: uid=egroupware-ucs5backup,cn=egroupware,dc=univention,dc=intranet
dn: uid=egroupware-ucs5backup,cn=egroupware,dc=univention,dc=intranet
changetype: modify
delete: krb5PasswordEnd
dn: uid=egroupware-ucs5backup,cn=egroupware,dc=univention,dc=intranet
changetype: modify
delete: shadowMax
Step 3
Install the above file:
ldapmodify -c -D uid=Administrator,cn=users,$(ucr get ldap/base) -W -f user.ldif
Enter LDAP Password:
modifying entry "uid=egroupware-ucs5backup,cn=egroupware,dc=univention,dc=intranet"
modifying entry "uid=egroupware-ucs5backup,cn=egroupware,dc=univention,dc=intranet"
Results:
UDM
udm users/user list --filter uid=egroupware-ucs5backup | grep -iE "passwordexpiry|dn"
DN: uid=egroupware-ucs5backup,cn=egroupware,dc=univention,dc=intranet
gidNumber: 5000
passwordexpiry: None
LDAP
univention-ldapsearch -LLL uid=egroupware-ucs5backup | grep -iE "shadow|krb5password"
objectClass: shadowAccount
shadowLastChange: 20487
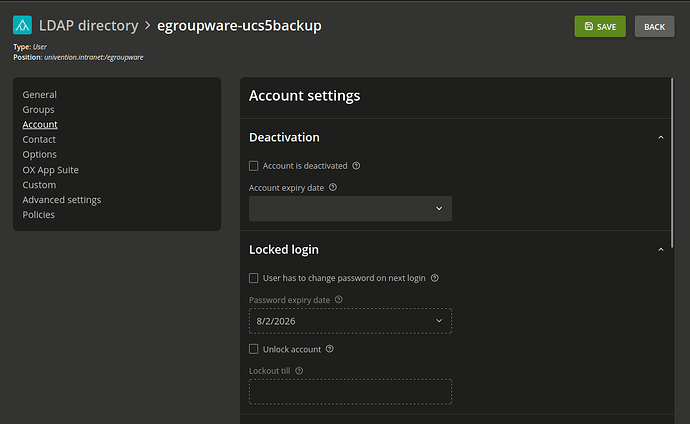
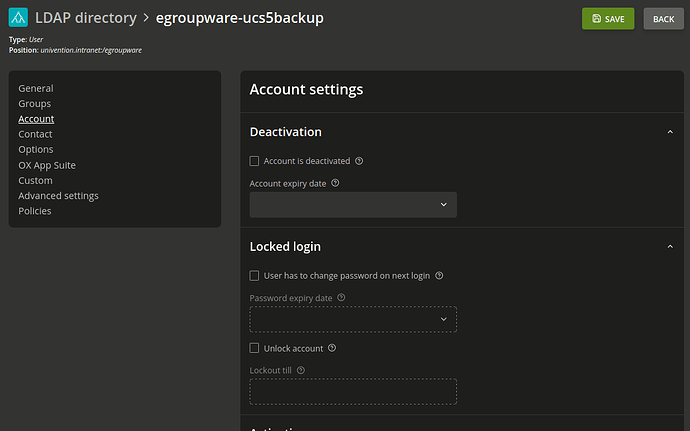
UMC