Hi Nitin,
from the information you provided I assume that you want to setup UCS as part of the AD child domain, i.e. the first option described in the manual, and not the second option described there. Please note that the first option implies that is finally intended to be the same as .
I’ve looked at the code and the original desgin decisions behind it. This is what I found:
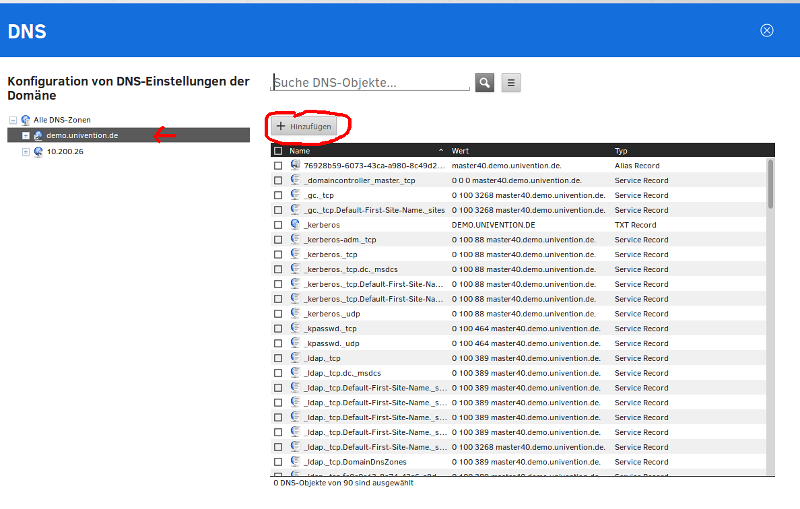
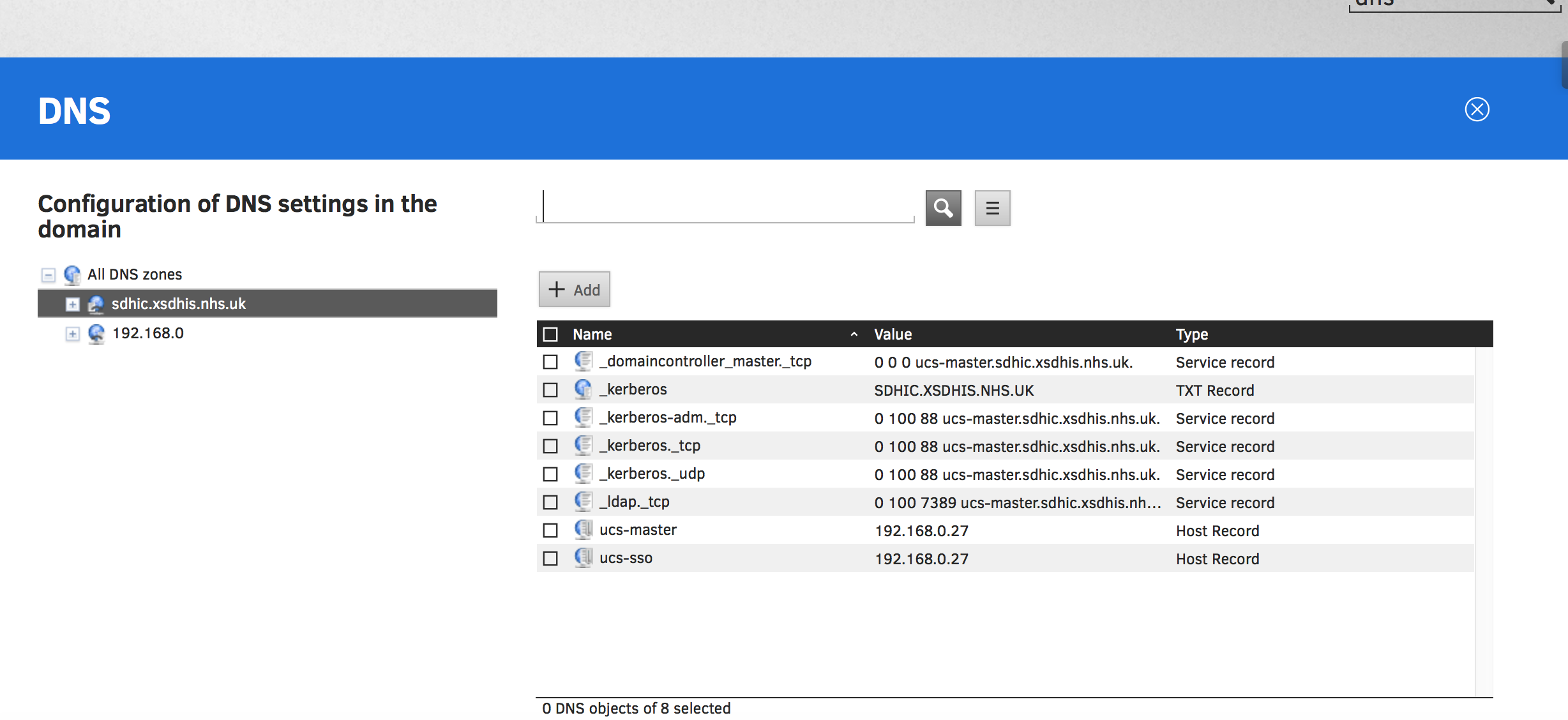
You are right, in this case the code currently tries to confirm that the given AD-DC is also a nameserver. We made that restrictive assumption because, for this first option of the AD-Connection, we later want to create these DNS records:
_domaincontroller_master._tcp.<child-dns-domain> SRV 0 0 0 <ucs-master-hostname>.<child-dns-domain>. ## mind the trailing dot
ucs-sso.<child-dns-domain> A <IP of UCS-Server>
From my quick look at the code I have the impression that the this “dig” check could be avoided, if those records have already been created manually in your parent domain DNS server. To confirm that after manually adding them, the following commands can be run on the UCS commandline and they must return the correct values:
dig "_domaincontroller_master._tcp.$(hostname -d)" SRV @10.181.8.11 +short
dig "ucs-sso.$(hostname -d)" @10.181.8.11 +short
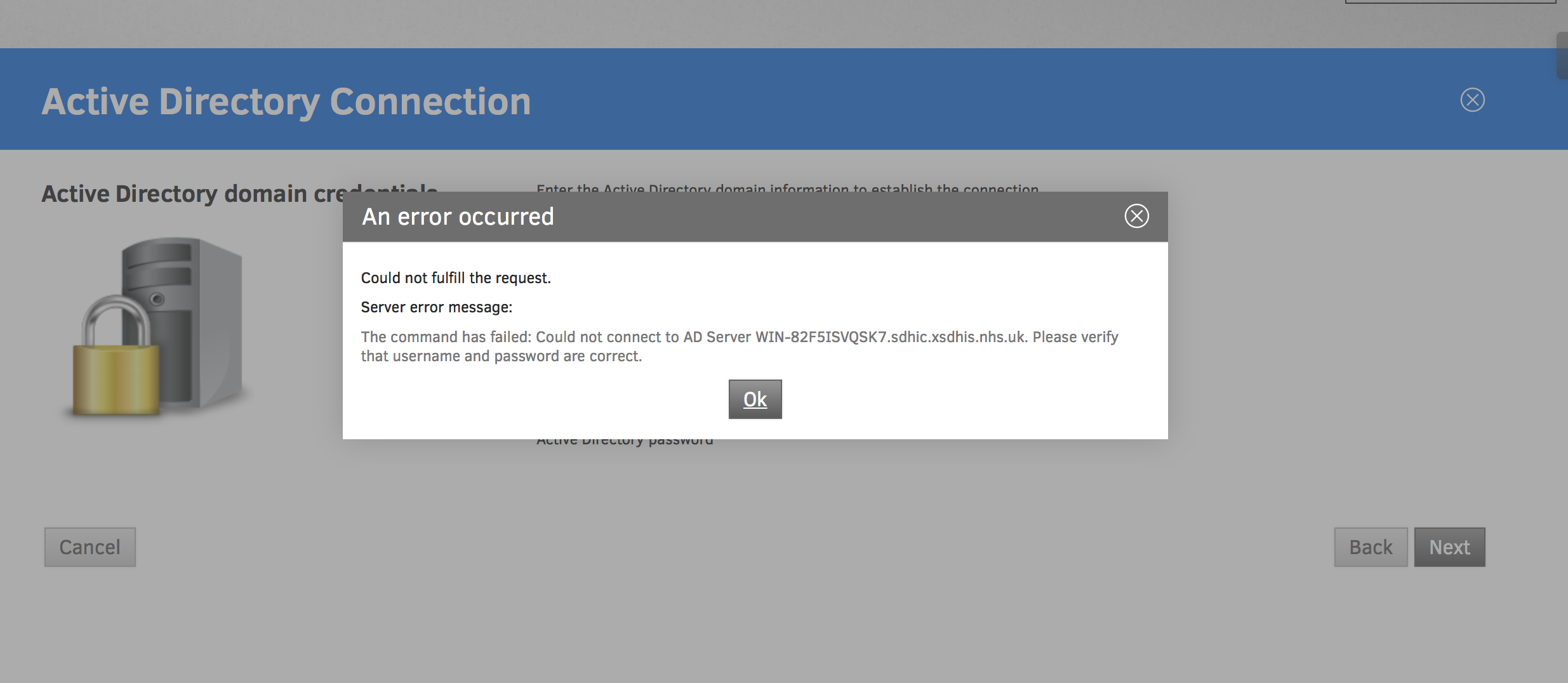
Iff these prerequisites are fulfilled, then we actually (AFAICS) wouldn’t need to perform the nameserver check via dig. The problem is, that this check is currently hardcoded in the python source code. Speaking as a developer (not a supporter) I share my assumption that it might be possible to quickly adjust this locally on your machine. This step would require that your are confident to use an editor like “vim” on a file containing Python source code, without causing any collateral damage. I would recomend you first copy that file to a safe location to be able to recover in case something got messed up:
cp /usr/share/pyshared/univention/lib/admember.py /var/tmp/admember.py.bak
After this precautionary step, you can open that file with an editor of your choice and change the line
def lookup_adds_dc(ad_server=None, ucr=None, check_dns=True):
into:
def lookup_adds_dc(ad_server=None, ucr=None, check_dns=False):
Without a test envirnment I cannot guarantee that this will have the desired effect.
Thanks for sharing you issue anyway, it helps to identify the relevance of a use case that was out of our initial focus.
We will consider your feedback to see how we can improve the product to make it usable without any hickups also in scenarios like yours.