Hello,
yesterday I upgraded my UCS 5.0-2 to 5.0-8 errata 1109 and also did upgrade Collabora CODE to 24.04.6.2 and Nextcloud to 28.0.7-0 as the latest versions
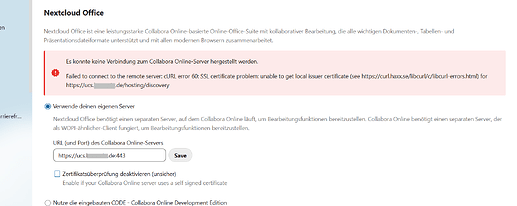
But now I get an error “Failed to connect to the remote server: cURL error 60: SSL certificate problem: unable to get local issuer certificate (see libcurl - Error Codes) for https://ucs.mydomain.de/hosting/discovery”, if I try to open an office document.
The linked page curl.haxx.se tells nothing but only lists the possible error codes and a sort explanation without hints to solution.
The page https://ucs.mydomain.de/hosting/discovery shows the mime-types listed in an xml-file.
All my certificates (Letsencrypt and CA) are up-to-date.
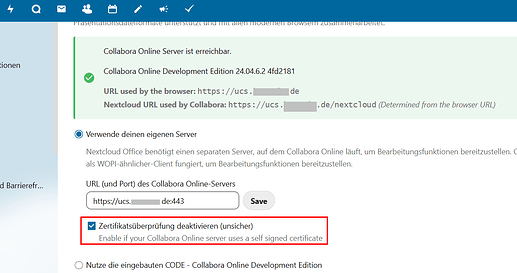
At the moment I must activate not to check the certificate:
otherwise I get an error message:
I did no changes in the Apache proxy-settings(default-ssl.conf):
…
ProxyPass /nextcloud http://127.0.0.1:40000/nextcloud retry=0
ProxyPassReverse /nextcloud http://127.0.0.1:40000/nextcloud
…
Apache log:
POST /nextcloud/index.php/apps/richdocuments/ajax/admin.php HTTP/1.1" 500 1192 “-” “Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:129.0) Gecko/20100101 Firefox/129.0”
I could not find any solution in this forum as well as in Nextcloud-forum how to fix it.
Nextcloud.log:
{“reqId”:“fmnXnGdwKlyJSOwyEhG6”,“level”:3,“time”:“2024-08-29T15:33:05+00:00”,“remoteAddr”:“84.xxx.yyy.61”,“user”:“< username >”,“app”:“richdocuments”,“method”:“GET”,“url”:“/nextcloud/apps/richdocuments/settings/check”,“message”:“cURL error 60: SSL certificate problem: unable to get local issuer certificate (see libcurl - Error Codes) for https://ucs.mydomain.de/hosting/discovery",“userAgent”:"Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:129.0) Gecko/20100101 Firefox/129.0”,“version”:“28.0.7.4”,“exception”:{“Exception”:“GuzzleHttp\Exception\RequestException”,“Message”:“cURL error 60: SSL certificate problem: unable to get local issuer certificate (see libcurl - Error Codes) for https://ucs.mydomain.de/hosting/discovery",“Code”:0,“Trace”:[{“file”:“/var/www/html/3rdparty/guzzlehttp/guzzle/src/Handler/CurlFactory.php”,“line”:158,“function”:“createRejection”,“class”:“GuzzleHttp\\Handler\\CurlFactory”,“type”:“::”,“args”:["*** sensitive parameters replaced “]},{“file”:”/var/www/html/3rdparty/guzzlehttp/guzzle/src/Handler/CurlFactory.php",“line”:110,“function”:“finishError”,“class”:“GuzzleHttp\Handler\CurlFactory”,“type”:“::”},{“file”:“/var/www/html/3rdparty/guzzlehttp/guzzle/src/Handler/CurlHandler.php”,“line”:47,“function”:“finish”,“class”:“GuzzleHttp\Handler\CurlFactory”,“type”:“::”},{“file”:“/var/www/html/3rdparty/guzzlehttp/guzzle/src/Middleware.php”,“line”:137,“function”:“__invoke”,“class”:“GuzzleHttp\Handler\CurlHandler”,“type”:“->”},{“file”:“/var/www/html/lib/private/Http/Client/DnsPinMiddleware.php”,“line”:121,“function”:“GuzzleHttp\{closure}”,“class”:“GuzzleHttp\Middleware”,“type”:“::”,“args”:[" sensitive parameters replaced “]},{“file”:”/var/www/html/3rdparty/guzzlehttp/guzzle/src/PrepareBodyMiddleware.php",“line”:35,“function”:“OC\Http\Client\{closure}”,“class”:“OC\Http\Client\DnsPinMiddleware”,“type”:“->”,“args”:[" sensitive parameters replaced “]},{“file”:”/var/www/html/3rdparty/guzzlehttp/guzzle/src/Middleware.php",“line”:31,“function”:“__invoke”,“class”:“GuzzleHttp\PrepareBodyMiddleware”,“type”:“->”},{“file”:“/var/www/html/3rdparty/guzzlehttp/guzzle/src/RedirectMiddleware.php”,“line”:71,“function”:“GuzzleHttp\{closure}”,“class”:“GuzzleHttp\Middleware”,“type”:“::”,“args”:[" sensitive parameters replaced “]},{“file”:”/var/www/html/3rdparty/guzzlehttp/guzzle/src/Middleware.php",“line”:63,“function”:“__invoke”,“class”:“GuzzleHttp\RedirectMiddleware”,“type”:“->”},{“file”:“/var/www/html/3rdparty/guzzlehttp/guzzle/src/HandlerStack.php”,“line”:75,“function”:“GuzzleHttp\{closure}”,“class”:“GuzzleHttp\Middleware”,“type”:“::”,“args”:[" sensitive parameters replaced “]},{“file”:”/var/www/html/3rdparty/guzzlehttp/guzzle/src/Client.php",“line”:331,“function”:“__invoke”,“class”:“GuzzleHttp\HandlerStack”,“type”:“->”},{“file”:“/var/www/html/3rdparty/guzzlehttp/guzzle/src/Client.php”,“line”:168,“function”:“transfer”,“class”:“GuzzleHttp\Client”,“type”:“->”},{“file”:“/var/www/html/3rdparty/guzzlehttp/guzzle/src/Client.php”,“line”:187,“function”:“requestAsync”,“class”:“GuzzleHttp\Client”,“type”:“->”,“args”:[" sensitive parameters replaced ***”]},{“file”:“/var/www/html/lib/private/Http/Client/Client.php”,“line”:230,“function”:“request”,“class”:“GuzzleHttp\Client”,“type”:“->”},{“file”:“/var/www/html/apps/richdocuments/lib/Service/DiscoveryService.php”,“line”:109,“function”:“get”,“class”:“OC\Http\Client\Client”,“type”:“->”},{“file”:“/var/www/html/apps/richdocuments/lib/Service/ConnectivityService.php”,“line”:44,“function”:“fetchFromRemote”,“class”:“OCA\Richdocuments\Service\DiscoveryService”,“type”:“->”},{“file”:“/var/www/html/apps/richdocuments/lib/Controller/SettingsController.php”,“line”:70,“function”:“testDiscovery”,“class”:“OCA\Richdocuments\Service\ConnectivityService”,“type”:“->”},{“file”:“/var/www/html/lib/private/AppFramework/Http/Dispatcher.php”,“line”:230,“function”:“checkSettings”,“class”:“OCA\Richdocuments\Controller\SettingsController”,“type”:“->”},{“file”:“/var/www/html/lib/private/AppFramework/Http/Dispatcher.php”,“line”:137,“function”:“executeController”,“class”:“OC\AppFramework\Http\Dispatcher”,“type”:“->”},{“file”:“/var/www/html/lib/private/AppFramework/App.php”,“line”:184,“function”:“dispatch”,“class”:“OC\AppFramework\Http\Dispatcher”,“type”:“->”},{“file”:“/var/www/html/lib/private/Route/Router.php”,“line”:315,“function”:“main”,“class”:“OC\AppFramework\App”,“type”:“::”},{“file”:“/var/www/html/lib/base.php”,“line”:1069,“function”:“match”,“class”:“OC\Route\Router”,“type”:“->”},{“file”:“/var/www/html/index.php”,“line”:39,“function”:“handleRequest”,“class”:“OC”,“type”:“::”}],“File”:“/var/www/html/3rdparty/guzzlehttp/guzzle/src/Handler/CurlFactory.php”,“Line”:211,“message”:“cURL error 60: SSL certificate problem: unable to get local issuer certificate (see libcurl - Error Codes) for https://ucs.mydomain.de/hosting/discovery",“exception”:[],“CustomMessage”:"cURL error 60: SSL certificate problem: unable to get local issuer certificate (see libcurl - Error Codes) for https://ucs.mydomain.de/hosting/discovery"},“id”:"66d1beeeb3715”}