Hi all,
we’re facing a strange behavior concerning dnsEntryZoneForward in our environment (UCS 4.4-6, samba4, samba4 DNS backend).
We added some new Windows 10 clients to the UCS domain. Each of them had 2 IP adresses (Both ethernet and wifi). Within weeks we noticed that some clients lost their DNS-forward records. That leads to the problem, that software like antivirus servers or opsi, couldn’t reach these clients anymore.
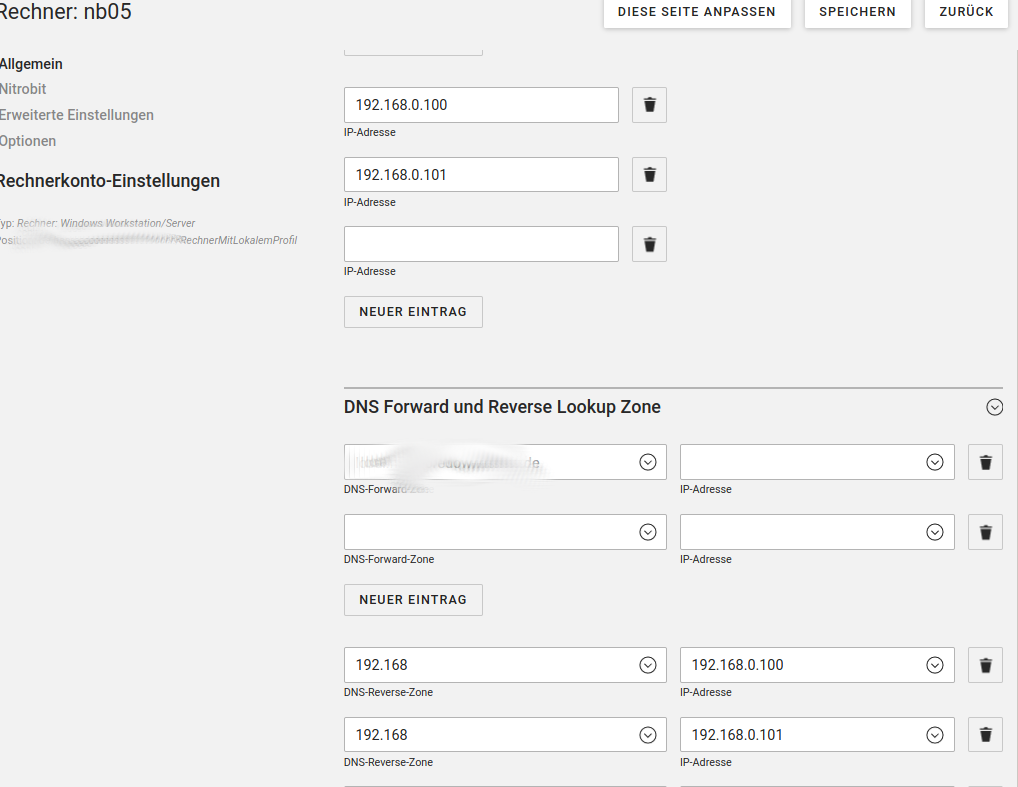
In UMC you can see the empty entries:
With udm it looks like that:
dnsEntryZoneForward: zoneName=some.domain.de,cn=dns,dc=some,dc=domain,dc=de 192.168.113.12
dnsEntryZoneReverse: zoneName=168.192.in-addr.arpa,cn=dns,dc=some,dc=domain=de 192.168.0.180
dnsEntryZoneReverse: zoneName=168.192.in-addr.arpa,cn=dns,dc=some,dc=domain,dc=de 192.168.0.209
The IP 192.168.113.12 was the clients adress, when it was connected via VPN. Of course that 192.168.113 subnet is not managed by our UCS servers. I’d like to know if there is a way to tell these clients not to change the zone-entries in UCS?
Cheers
Sebastian